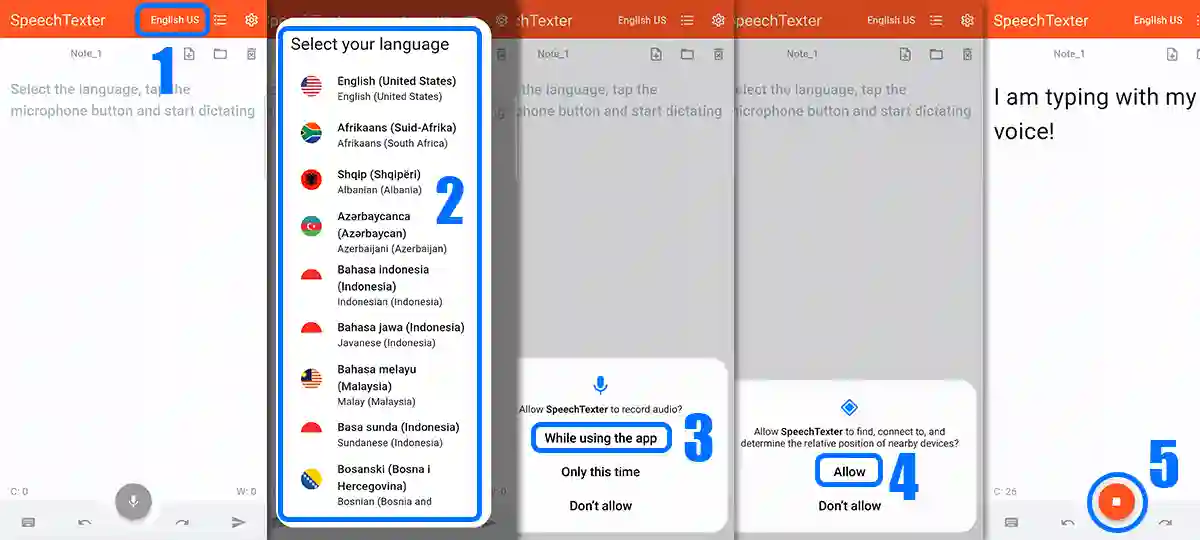
SpeechTexter is a free multilingual speech-to-text application aimed at assisting you with transcription of notes, documents, books, reports or blog posts by using your voice. This app also features a customizable voice commands list, allowing users to add punctuation marks, frequently used phrases, and some app actions (undo, redo, make a new paragraph).
SpeechTexter is used daily by students, teachers, writers, bloggers around the world.
It will assist you in minimizing your writing efforts significantly.
Voice-to-text software is exceptionally valuable for people who have difficulty using their hands due to trauma, people with dyslexia or disabilities that limit the use of conventional input devices. Speech to text technology can also be used to improve accessibility for those with hearing impairments, as it can convert speech into text.
It can also be used as a tool for learning a proper pronunciation of words in the foreign language, in addition to helping a person develop fluency with their speaking skills.

Accuracy levels higher than 90% should be expected. It varies depending on the language and the speaker.
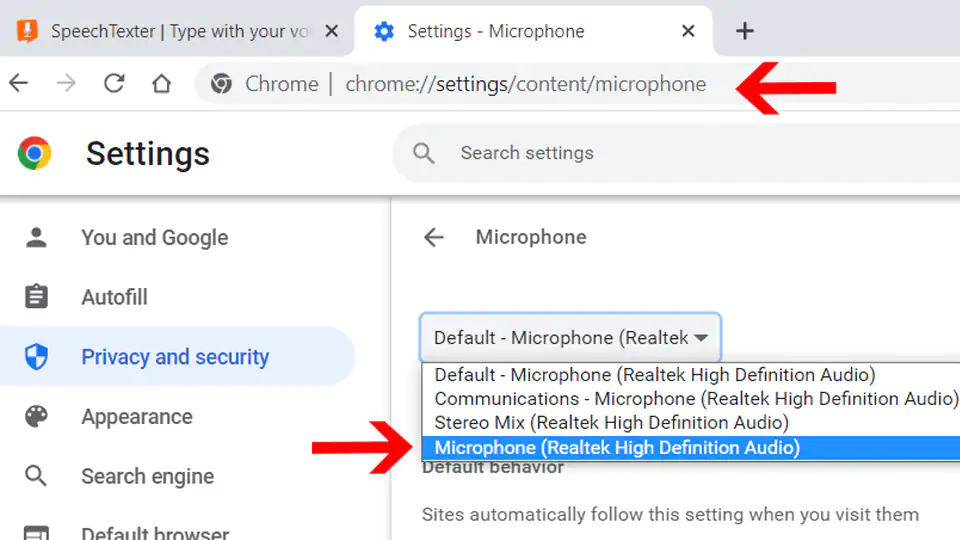
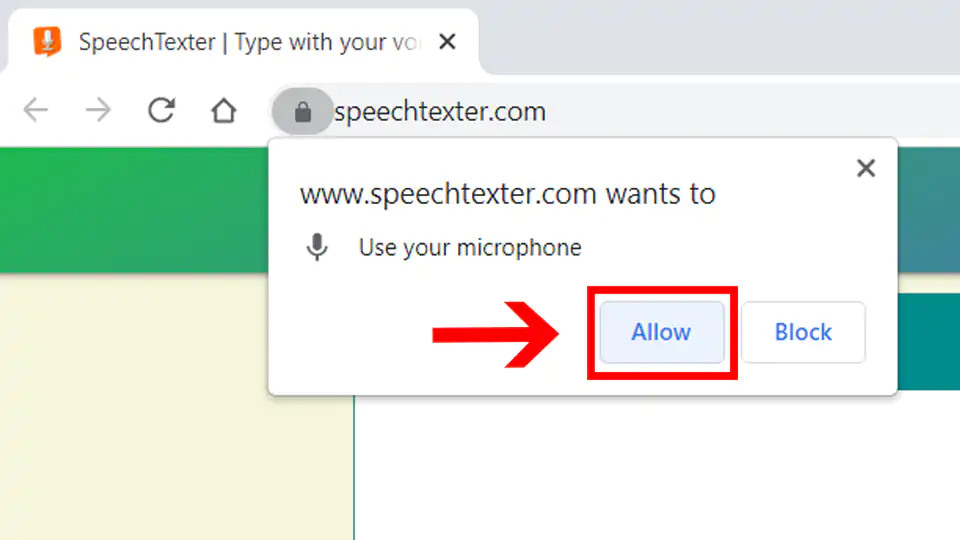
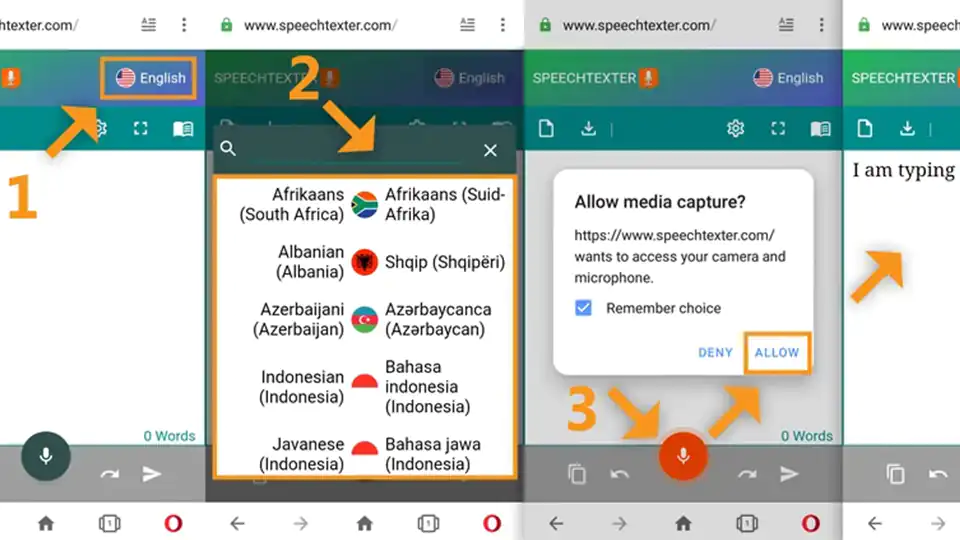
No download, installation or registration is required. Just click the microphone button and start dictating.
Speech to text technology is quickly becoming an essential tool for those looking to save time and increase their productivity.